The Pane Network
The pane Network can be used to replace the functions that have been lost from the previous Network Utility which had been part of the operating system in older versions of macOS. TinkerTool System provides a similar range of functions and additionally contains modernized features, in particular to support today’s default network protocol IPv6.
Information About Network Interfaces
You can review technical details and statistics on all network interfaces of your Mac that are currently active. Active means that at least one IPv4 or IPv6 address has been assigned to the network port which can be used to communicate with other devices. The get the data, perform the following steps:
- Open the tab item Info on the pane Network.
- Use the pop-up button to select the interface for which you like to get information.
The items shown in the window are automatically updated every 10 seconds.

The following details are available:
- Hardware Address: the predefined address built into the hardware of the network port, used for communication at the Media Access Control (MAC) level. This address is also called MAC address.
- IPv4 Address: the currently assigned address for Internet Protocol version 4.
- Link Speed: the detail type of the network connection. The exact meaning is determined by the kind of network port. In most case, the currently selected data rate will be shown.
- Link Status: the current status of the network connection as defined by the operating system.
- Vendor: the manufacturer of the physical hardware port
- Model: the type of port or its hardware model number
- IPv6 Addresses: the currently assigned addresses for Internet Protocol version 6.
- Sent Packets: the number of data packets that have been sent since the operating system was started.
- Send Errors: number of sent packets for which an error was detected.
- Received Packets: the number of data packets that have been received since the operating system was started.
- Receive Errors: number of packets received for which an error was detected.
- Collisions: for network technologies where it is possible that multiple devices send data unsynchronized at the same time, which causes data packets to interfere with each other, the number of cases where such transmission collisions have occurred.
Routing Tables and Network Statistics
Via the item Netstat, you can review further statistics from the network management of macOS, relevant for all network ports.
- Open the tab item Netstat on the pane Network.
- Select one of the radio buttons to choose the item for which you like to retrieve data.
- Click the button Netstat.
The application will determine the information and show it in an additional dialog sheet. You can also print the results or save them as text file.
Please note that macOS may need several minutes of computation time before data will be shown. The information comes directly from the UNIX level of the operating system.
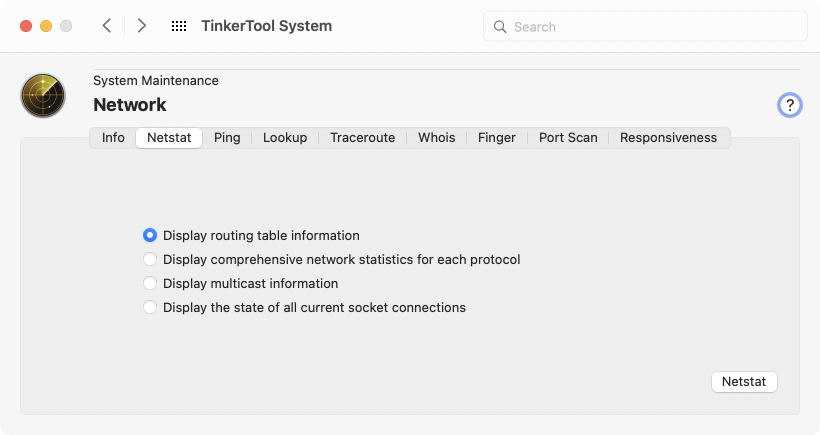
The following statistics are available:
- the routing table of the operating system: the table indicates which interface port is used to communicate with which destinations, or address ranges, respectively. This means this table decides for each outgoing network packet which interface port will be selected for the transmission.
- statistics for each communication protocol: sorted by the typical transmission protocols, like TCP, UDP, IPv4, ICMP, IGMP, IPsec, IPv6, ICMP6, and IPsec6, this item will show statistics about the number of transferred packets, errors, fragmentation, memory use, and similar data.
- statistics on membership in multicasts: Multicasts are network transmissions that are received simultaneously by a whole group of devices.
- statistics related to logical network connections (sockets) that are currently established: a table shows all endpoints to which communication links are currently established in the network.
Checking Network Connections via Echo Signals
To check the connection to another device in the network, it can be useful to send this device a request to report back. A test packet is sent to the other device, asking to reflect it like an echo. From the technical slang of working with echo sounders (sonars), sending a test signal back and forth is called ping.
Perform the following steps to run such a communication test:
- Open the tab item Ping on the pane Network.
- Enter the desired destination into the text field either by address or by name and press the return key.
- Check the field Use IPv6 protocol if the test should not be performed based on IPv4, but based on IPv6.
- Choose whether a specific number of test signals should be sent, or whether the test should run endlessly until you click the Stop button.
- Click the Ping button.
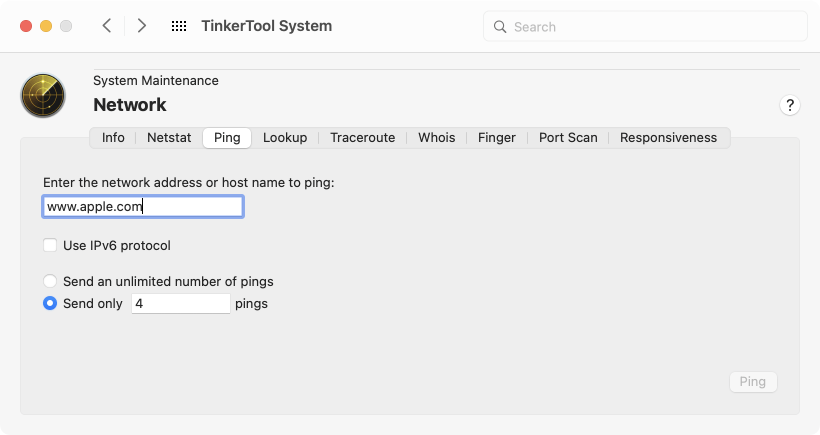
The report that is shown during the individual ping signals indicates how many bytes have been sent to which address, the current running number of this signal (icmp_seq, Internet Control Message Protocol sequence number), the maximum number of intermediate stations the sent packets are allowed to pass (ttl, time-to-live), and how long (in milliseconds) it took until the echo came back again (time). An additional summary is shown at the end of the report, indicating among other things, how many test packets have been sent, as well as the minimum, average, and maximum echo times, together with their standard deviation during the entire test.
Not all devices will respond to ping requests. For security or performance reasons, some devices may refuse to answer. Such a case cannot be distinguished directly from cases where the destination host could actually not be reached.
You can use the normal copy/paste or drag-and-drop features of macOS when you like to transfer an address or computer name into the text field. Note however, that a paste operation won’t be accepted if you try to transfer text containing characters that are officially forbidden by the Internet standards, an underscore (_), for example. TinkerTool System doesn’t perform a full syntax check, but may reject pasted text with characters not compliant with the rules of RFC 952.
Other fields in the Network pane for entering addresses or host names also follow this policy.
Determine the Assignment Between Host Names and Addresses
The Domain Name Service (DNS) is designed to make it possible to reach other devices in the network not only by their addresses, but also by their names. This service either looks up the name for a valid address, or in reverse direction, determines the assigned name(s) for an address. You can submit such a request to the service manually any time. To do this, perform the following steps:
- Open the tab item Lookup on the pane Network.
- Enter either the name of the device, or its IPv4 address, or its IPv6 address into the text field and press the return key. This will be interpreted as request to look up the missing parts via DNS.
- If you like to receive a lot more details about the internal query sent and the associated response from DNS in addition to the plain answer to your request, check the field Use “dig” for more detailed information.
- In case you have selected the detailed variant in item (3.), you can additionally choose whether you like the request to be sent via IPv6 only, and whether the IPv6 address should be looked up as well.
- Click the button Lookup.
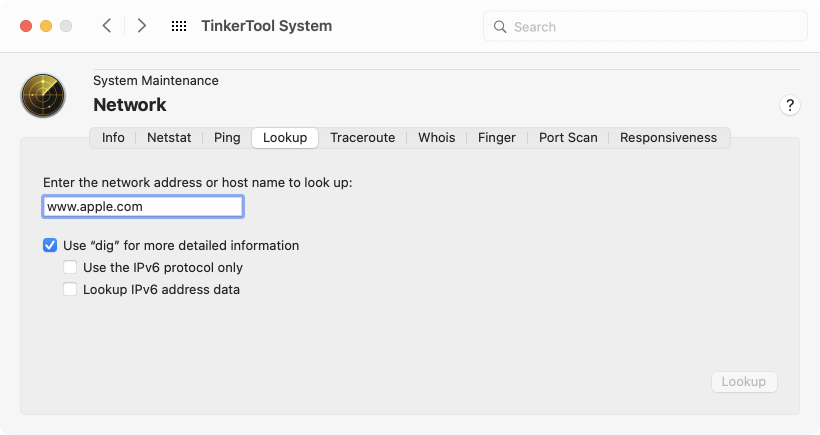
The response contains in each case
- which server (with its name and address) has sent the answer, and
- how the answer is, i.e. name(s) and address(es).
To evaluate the lookup request, the system will use the DNS server currently configured in the network preferences of macOS.
Trace the Path of Data Packets
In larger networks such as the Internet, destination points can only be reached if the data packets can travel along multiple intermediate stations. The individual nodes of the network determine the currently best route, based on network maps, connection costs, and current utilization of the network components. It can be interesting to display the currently selected route for communication with a specific destination. This operation is known as packet tracing or traceroute.
- Open the tab item Traceroute on the pane Network.
- Enter either name or address of the destination into the text field and press the return key.
- Click the button Trace.
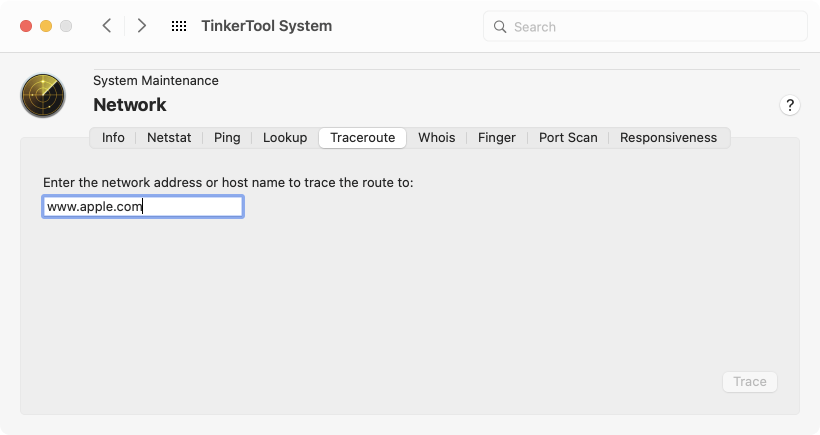
The current route is determined and measured using a series of test data packets (similar to the ping operation). For each intermediate station, called hop, you will get one line of output. If available, it will indicate its name and address, as well as the transmission times to reach the next node. Determining the entire route can take a few seconds. Data that cannot be retrieved at the moment is replaced by asterisks.
Querying Databases of the Whois Service
On the Internet, names of the individual network devices, or their ports, respectively, are assigned using a hierarchical system. The names are registered for a fee at specific registration authorities. These registries establish the whois service, a database that lists all domain names currently in use. The databases can be accessed publicly to determine information about the owner of a name, a contact person for administration, a contact for technical questions, one for name abuse, the date of registration and the validity period, the responsible registration authority, and the authoritative DNS service.
For data protection reasons, not all of this information can be retrieved in each country or from every registration authority. The amount of available data can vary greatly depending on the domain name.
To find information about a registered domain name, perform the following steps:
- Open the tab item Whois on the pane Network.
- Enter the domain name into the text field and press the return key.
- From the overview of whois servers, select the server which presumably belongs to the responsible registration authority for that domain, or enter the name of another whois server.
- Click the button Whois.
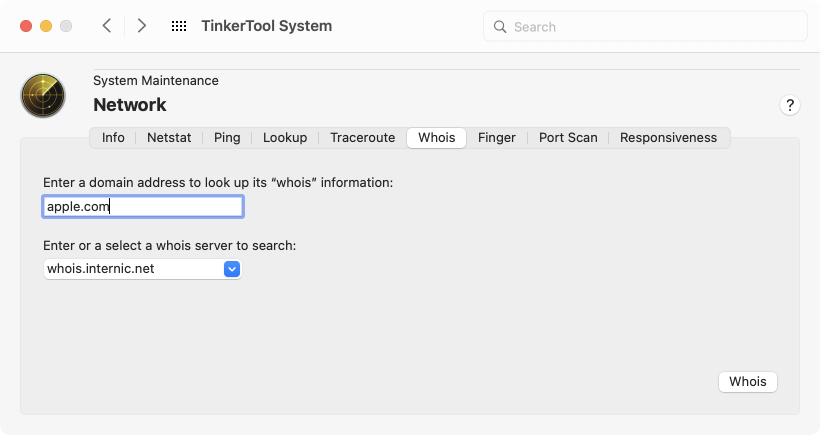
The publicly available data provided by the selected whois service will be shown. As always, you can print the result or save it as text file.
Determining User Information via the Finger Service
The finger protocol describes an information service that provides data about network users live, mainly to determine how and where a user can be reached within a company or similar organization. In addition to contact details, such as phone numbers, room numbers, or email addresses, finger is designed to indicate at which computer of the network a user is currently logged on, and for how long. Querying the finger service is done via text patterns similar to email addresses, namely
name@domain
where name is the short account name of the user, and domain is the domain name of the network.
Perform the following steps to get finger data about a network user:
- Open the tab item Finger on the pane Network.
- Enter the finger specification into the text field and press the return key.
- Click the button Finger.

The finger protocol was developed between 1971 and 1977 and is considered obsolete. For data protection reasons, as well as for labor law and security reasons, it is rarely used today. If it is actually used, data will usually be available in the local network only, not across the Internet.
If the finger service is unavailable, you will typically receive an error response that includes the message
finger: connect: Connection refused.
Scan for Open IPv4 Ports
Addresses are used to contact specific network devices, or their network ports, respectively. Port numbers are used to contact specific communication end points (sockets) on a network device. Such a port provides a certain service in the network and is addressed by using an assigned number between 0 and 65,535. For example, DNS servers that have been mentioned in this chapter usually provide their service at port 53 of the respective server computer. An encrypting web server (HTTP over SSL) typically offers its service on port 443.
It is technically possible to check whether a certain network device has opened a port on a specific number, even without sending actual payload requests to this port. This way, it is indirectly possible to determine whether a device provides the service that usually belongs to that port number, and whether that service can be reached. By testing a range of port numbers, it will be possible to spy out which network services are likely to be expected on a particular device. This does not need to be known in advance.
On the other hand, if a certain service should not be publicly visible for specific networks, this technique can also be used to verify that the associated port has been blocked successfully, and its service cannot be reached. Searching for open port numbers is called port scanning. Perform the following steps to conduct a port scan:
- Open the tab item Port Scan on the pane Network.
- Enter the destination either by IPv4 address or by name into the text field and press the return key.
- Select whether you like to have all possible ports checked, or only a specific range of numbers. It is valid if the range only contains a single number, for example specifying “between 80 and 80”.
- Click on the button Scan.
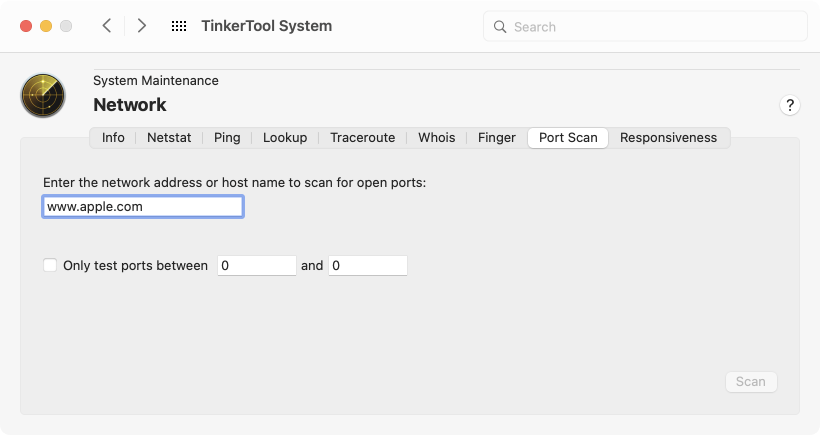
Warning: Do not use this feature unless you have permission from the owner of the destination computer. Due to the aforementioned espionage possibilities, a port scan can be considered a malicious act if used for a device of a foreign network. Its owner or your Internet provider could take legal or technical countermeasures.
Responsiveness (macOS 12 or later only)
This feature is not offered by macOS 11 Big Sur.
macOS contains a built-in speed test that is able to assess the quality of your local network and its Internet connection. You can run the test, which usually takes less than half a minute, via a simple mouse click. The test basically estimates how well your Internet connection will react when several devices or applications are using it at the same time. The results of the test can be particularly useful if you are using an Internet gateway whose performance can be optimized manually, for example by configuring features such as Smart Queue Management (SCM). You can run several tests under similar conditions to experiment which changes lead to better performance.
Please note that both, the network between this computer and your Internet gateway (“router”), the network between the gateway and your Internet provider, as well as the link between your provider and the Internet are part of the measurement. macOS records the following metrics during the test:
- Upload capacity: the current net throughput when sending data to the Internet
- Download capacity: the current net throughput when receiving data from the Internet
- Upload flows: the maximum number of typical Internet send connections possible simultaneously until the network is fully utilized
- Download flows: the maximum number of typical Internet reception connections possible simultaneously until the network is fully utilized
- Responsiveness: the maximum number of packet round-trips per minute that can be expected during typical transactions, when multiple programs send inquiries and wait for replies from the network. A higher number means higher quality of the “felt” network behavior.
- Overall quality assessment by macOS: a summary of the total result as a simple catchphrase (see below).
During the measurement, a large amount of test data is transferred between your computer and one or more Apple Internet servers. Which servers are involved can be dynamically controlled by Apple and change any time.
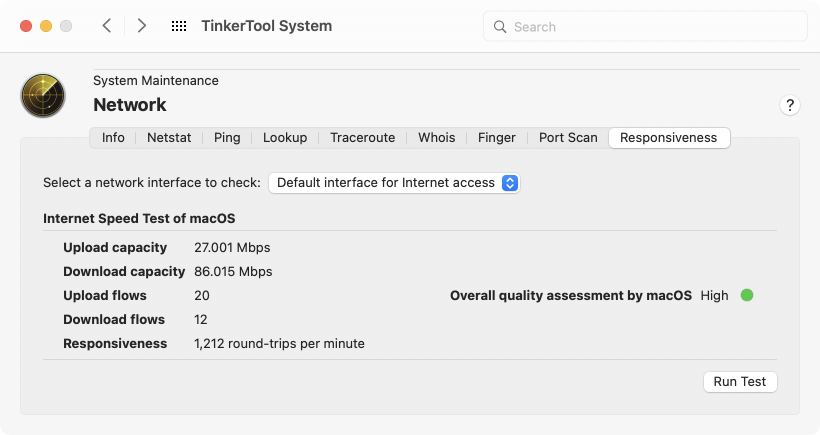
Perform the following steps to get an overall assessment of your network quality:
- Make sure that the pop-up button Select a network interface to check is set to the desired option. TinkerTool System offers all physical and virtual network interfaces that currently have an active IP address. Please note that not all interfaces are usually connected to the Internet, so they cannot be used for testing. Usually, it is sufficient to keep the selection Default interface for Internet access which causes macOS to automatically choose the network link currently in use for Internet data transfers.
- Click the button Run Test.
The test will then be run by macOS and TinkerTool System will show its results. The overall assessment is at the discretion of macOS and is not influenced by TinkerTool System. Apple provides the following documentation to understand the end result:
- Low: If any device on the same network is, for example, downloading a movie or backing up photos to iCloud, the connection in some apps or services might be unreliable, like during FaceTime video calls or gaming.
- Medium: When multiple devices or apps are sharing the network, you might see momentary pauses or freezes, like during FaceTime audio or video calls.
- High: Regardless of the number of devices and apps sharing the network, apps and services should maintain good connection.