macOS as NFS Server
Sharing Data via NFS
macOS can share folders of its own file system for access in the network via the NFS protocol.
NOTE: NFS and UNIX systems often use the word export to refer to an NFS share. This manual and NFS Manager are using the term share only.
When sharing files, Apple’s NFS server will offer them via the NFSv2 and NFSv3 protocols.
Due to the architecture of NFS to be designed as a distributed file system, it is common
- to share whole disk volumes or specific “top-level” folders of volumes and
- to share private home folders.
The access privileges for users and groups are controlled by the permission settings of each single file and folder, not by settings for the share. A share can only define access restrictions for computers.
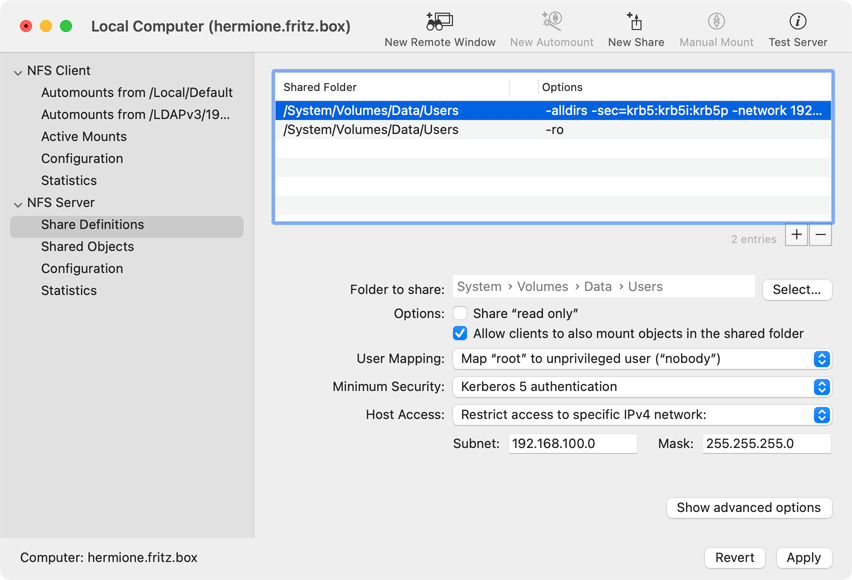
Creating or changing NFS shares
To work with NFS shares, select the item NFS Server > Share Definitions in the left overview column of the control window, or select the menu item Configuration > Show Share Definitions. The list of shared folders will be displayed in a table at the right side of the window. After selecting a line in the table, detail information about this share will be shown below the table. This data can be modified as desired.
- To delete a share, select the respective line in the list and click the button [—] below the table.
- To create a new share, click the button [+] below the table. A new share entry will be created with defaults that you’ll have to overwrite.
Perform the following steps to adjust the settings of a share to your needs:
- Click the button Select… next the to the line Folder to share to choose a local folder which should be made available to the network. Please also see the notes below in the section “Limitations of NFS shares”.
- Use the other controls to define the settings for this share.
If all write operations to this share should be blocked even if the respective user would have write permission, leave the checkmark at the field Share “read only” set. Otherwise you’ll have to remove the checkmark.
After a certain folder has been selected for sharing, its absolute path will become the share name other computers must use for mounting. Other computers will see the whole file hierarchy within (or “below”) that folder. If computers should additionally be allowed to mount a subfolder of the shared folder, check the option Allow clients to also mount objects in the shared folder. Example: Instead of /share other systems may also mount /share/subfolder if desired.
Mapping user and group accounts between client and server
The pop-up button User Mapping defines how users and groups of accessing computers should be mapped to users and groups of the sharing computer. The security model of NFS allows certain limitations:
- Map “root” to unprivileged user (“nobody”): The top system administrator (root) of a foreign computer should be seen as unauthorized user by the NFS server, mapping her to the account nobody which usually doesn’t have any rights. This is the recommended setting to avoid security holes.
- Map all users to unprivileged user (“nobody”): In this mode, all users and groups of an accessing computer will be mapped to the account nobody. This is a very secure setting.
- Don’t map users: This settings causes users and groups of the accessing computer to be mapped one-to-one to users and groups of the NFS server. This means the UIDs and GIDs will be used without further inspection or interpretation. In particular, the top system administrator (root) of each accessing computer will automatically be seen as top system administrator (root) of the NFS server. This can be a major security hole.
- Use customized setting (see advanced options): This setting allows to define advanced mappings manually. The button Show advanced options has to clicked (see below).
Security settings when using Kerberos
If your network defines a Kerberos realm and a respective Kerberos Key Distribution Center is available, NFS shares can be protected by additional security features and data transfer can be encrypted. The pop-up button Minimum Security specifies what security features an accessing computer (and Kerberos user) have to support at least to be granted access to this share.
- System standard only: This setting specifies that the use of Kerberos is not required. Mount and access operations will be performed in “classic UNIX style”, using UID and GID identifications only.
- Any available security mechanism: The client is allowed to freely choose between classic access and any methods protected by Kerberos.
- Kerberos 5 authentication: Only clients using Kerberos are granted access. The user and/or computer performing the mount has to be authenticated as being valid by Kerberos.
- Kerberos 5 authentication with integrity checks: Kerberos is required. In addition to the authentication of user and computer via Kerberos, the client has to ensure that each transferred NFS packet is protected against manipulation.
- Kerberos 5 with checks and encryption: Only clients which use Kerberos to authenticate users and computers, which perform integrity checks on each data package, and which additionally encrypt all packages are granted access. This is the most secure way to operate NFS. Due to the costly operations performed on each data packet, the overhead on both sides of the connection will increase however, the performance and effective speed might significantly decrease.
- Use customized setting (see advanced options): This permits to combine the previously mentioned Kerberos security features in any way you like. Click the button Show advanced options (see below) to disable or enable them separately.
Limit access to certain computers
Because NFS is designed as distributed file system and no authentication is needed, access to shared folders should be limited to well-defined “trusted” clients. The basic settings are defined by the pop-up button Access permission:
- Allow access from any network and computer: Access will not be restricted. Any computer which can contact the NFS server via network is allowed to access the share. This is a potential security risk. If the network in which the computer is located has not been isolated by a firewall against access from other networks, basically any connected network (potentially the whole Internet) may have access to the shared files.
- Restrict access to specific IPv4 network: You have to enter a subnet address with accompanying net mask. In that case, only computers using IP addresses of the specified subnet are allowed to access the share.
- Allow listed clients only (see advanced options): You can specify a list of IP addresses or DNS names. Only the listed computers are granted access. The list has to be entered in a panel which will be displayed after clicking the button Show advanced options.
Further options
Additional settings for the NFS share can be specified in a dialog window which will open after the button Show advanced options has been clicked. These options are described in detail on a separate page.
Special restrictions to consider when sharing files for video or audio media boxes
You may like to use the NFS server to share media files with your network, e.g. movies or music. The media can then be accessed by player devices (“media boxes”) connected to your TV or home-stereo equipment, under the condition the player supports the NFS protocol standard. Those players often underly certain limitations, because they don’t contain a fully featured operating system. For more information about typical problems experienced with media boxes in practice, please see this solutions page.
Repairing a damaged share configuration
If you have tried to configure the NFS server manually, without the help of NFS Manager, or if you have used a third-party application which is not perfectly adapted to your current version of macOS, the share configuration might have been damaged in a way that the NFS server shuts down completely. NFS Manager is capable of detecting this problem, giving you a chance to remove the broken configuration file, beginning with a new, empty one. In this case, all user interface elements of the item Share Definitions will be blocked and the message The current share configuration is invalid. will appear in red below the share table. Click the button More info… to open a special repair panel and display further details about the problem. You can either
- remove the bad configuration manually and inform NFS Manager about this change, or
- let NFS Manager erase the current configuration to begin anew with a clean, empty table of shares.
In case the problem details indicate that a shared folder has been removed or renamed, you can of course fix this problem by other means (e.g. recreating the missing folder with the Finder), then let NFS Manager re-read the configuration.
When erasing the current configuration, the invalid definition entries are saved to a backup file. You will find it at /etc/exports-INVALID.backup. Experienced system administrators can use this file to recover some of the previous share entries.
Limitations of NFS shares
When creating NFS shares, four basic rules must always be respected:
- In principle, any physical file system (in Macintosh terminology each disk volume of a hard drive) or one of its subfolders can be shared.
- Sharing a subfolder of a folder which is shared already is permitted only if this subfolder is located on a different physical file system. (This is the case if the shared folder contains the mount point of another volume.)
- Sharing a super-folder of a folder which is shared already is permitted only if this super-folder is located on a different physical file system.
- Only local file systems can be shared. (It is not permitted to share a file system mounted via network from another computer.)
Those four basic rules are based on the architecture of the NFS design. They always have to be fulfilled, no matter which operating system is used. In addition, the following rules apply when using macOS:
- macOS can only share file systems supporting permissions. For example it is not possible to share MS-DOS®-formatted file systems (FAT) via NFS in the network.
- A share entry can be specified multiple times only if different sets of computers are granted access permission in each entry. No overlaps or contradictions are permitted. For example you cannot share a folder for the computers A, B, C, and additionally share the same folder with different options for use by the computers A, D, E. In this case the role of the computer A would be undefined and contradictory.
- Some versions of macOS may not allow to define multiple shares per file system for security reasons. This means each volume can have a maximum of one NFS share only. NFS Manager makes you aware if this restriction may apply.
IMPORTANT: If one of these rules has been violated, macOS will reject the affected or even all shares. In that case, the NFS server won’t work as expected. NFS Manager tries to find violations of the rules in advance. When contradictory share definitions are found, error messages will be shown.