Evaluating Results
Overview of the Report Window
A typical report window is shown below. It will be opened by Sync Checker after at least one mismatching object has been detected during the comparison. The upper part of the window can be used to navigate through the list of differences, the lower part is used to display the exact details of a selected mismatch.
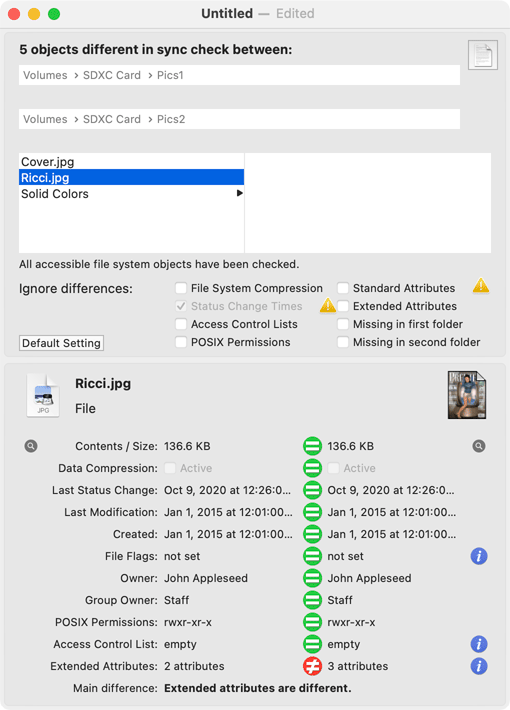
The headline shows the number of different objects found. The locations of the two folders that were checked follow after that. If a previously scanned archive was used as data source, this will be mentioned. Below that, you will find an object browser, similar to the column view of the macOS Finder. Objects at the top level of the compared folders appear in the first column, objects in a subfolder at this level appear in the second column, etc. When you click onto an object, the details of the mismatch will be displayed in the lower part of the window. A text line below the browser indicates whether an ignore list was in use.
In some cases, the text Intermediate folder or no object selected will be displayed as detail information. The term “intermediate folder” should mean that Sync Checker is displaying this folder in the browser only to understand where objects inside that folder are located, helping you to navigate through the hierarchy of nested folders. The selected folder itself has not been identified as a mismatch in this case, however.
The Mismatch Filter
The switches labeled Ignore differences below the browser represent a filter setting used to show or to hide selected types of mismatches. If you set a check mark here, the respective mismatch entries will no longer be displayed in the list. For example, if you set a check mark at Missing in second folder, the report window will only show mismatching objects which have other differences. Objects with the only difference that they are missing in the second folder will temporarily disappear from the list.
Depending on what advanced options you had chosen to perform the sync check operation, the corresponding options will be selected automatically in the ignore filter and cannot be changed. For example, if you had instructed Sync Checker not to consider file system compression when comparing objects, the switch at File System Compression will be on and cannot be changed. It is clear that mismatches regarding compression cannot be contained in the result list, so unhiding (“not filtering”) these entries doesn’t make sense in this case.
The button Default Setting can be used to establish Sync Checker’s recommended display filter. Mismatch types usually unimportant will be filtered, but all other types of differences will be displayed. In case the number of mismatches is very high, Sync Checker might need a few seconds to display the updated list after the filter settings have been changed.
If you have run a Quick Check, the mismatch filter won’t be shown.
The Mismatch Details
The display in the lower half of the window shows the details of the mismatch selected in the object browser. The items at the left correspond with the first folder of the sync check, the part at the right corresponds with the second folder. Equal signs in green between entries of the two columns show items which match, “not equal” signs between entries, marked in red, indicate a mismatch. At the top you’ll see the icons of the two mismatching objects, their name, and the general type of the objects, e.g. File or Folder.
Note that a mismatch between two corresponding objects may affect more than one aspect at the same time. The red and green equality markers always indicate all types of differences found, even if you have set the display filter to ignore certain mismatch types.
The following items are shown:
- Contents / Size: The size of the actual contents of the object. On file systems capable of storing forks, the size will represent the size of the data fork. If the report window shows that this item is differing although the two size values are identical, this will indicate that the contents of the objects must be different.
- Data Compression: A check mark at Active indicates whether invisible data compression at the file system level has been used to store this object.
- Last Status Change: Date and time when the status (attributes) of this item has been changed for the last time.
- Last Modification: Date and time when the contents of this item changed for the last time.
- Created: Date and time when this object has been created in the file system.
- File Flags: abbreviations for marker attributes which can be set or unset for objects at the Unix level of macOS. To show the markers in detail, click the info icon at the right (see below for further information).
- Owner: the full name of the user account which owns this object.
- Group owner: the full name of the user group which owns this object.
- POSIX Permissions: a code which represents the access permissions for owner, group owner and other users accessing this object. Sync Checker uses a shortened form of the codes commonly used on Unix systems to present the standard permission settings (r = read, w = write, x = execute/traverse). If you are not familiar with these codes, press the info icon to the right of this entry to display the permission settings in greater detail and in clear text (see below for further information).
- Access Control List: the number of Access Control Entries stored in the Access Control List of this object. An ACL can become rather large, so it won’t be possible to display it in detail at this location. Click the info icon at the right to display the ACL settings in full detail (see below for further information).
- Extended Attributes: the number of Extended Attributes stored for this object. There can be an unlimited number of attributes with arbitrary names and any values, unknown in advance. For this reason, it won’t be possible to display the attributes in detail at this location. Click the info icon at the right to display the full list of Extended Attributes (see below for further information).
- Main difference: The type of difference which Sync Checker considers to be the most important one when comparing the two corresponding objects.
Time Specifications
The time specifications for last status change, last modification and creation of a file system object are shown in the format you have specified for the language and region setting of the operating system. The common formats don’t consider fractions of a second. As mentioned in the chapter Comparing two Folders or Disks, some file systems store time specifications with a resolution of nanoseconds, however. If the sync check was executed with the option to respect time deviations of less that one second, the report window may indicate a respective time mismatch, but you may not see it directly.
To solve this problem, make sure the report window is active and in front, then hold the cursor over a time value. Sync Checker will then show the time specification as a help tag (“tool tip”), using the technical ISO 8601 standard. This standard is predefined to present the time with at least millisecond resolution.
The File Flags
After clicking the info icon next to the entry File Flags, Sync Checker will open an additional sheet, showing detail information about a set of attributes set at the Unix level. Check marks at the left correspond with the object of the the first folder, the switches at the right with the object from the second folder.
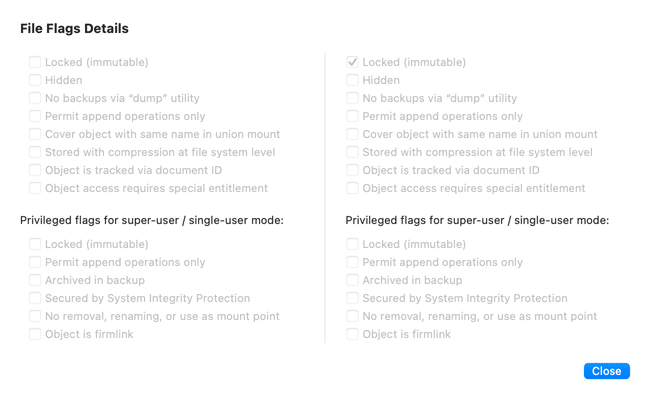
- Locked (immutable): This setting is used as a general protection against changes, independent of write permissions. When the setting is active, the object cannot be altered or deleted. The Finder uses a small lock icon next to the standard icon of the object to present such protected objects.
- Hidden: This setting is used to indicate that graphical applications like the Finder or the open/save panels of other applications should not display this object. It is invisible at the graphical user interface.
- No backups via “dump” utility: If this marker has been set, the object will be excluded from backup copies created by the Unix command-line program “dump”.
- Permit append operations only: When active, applications cannot delete or change the current contents of the file. Programs can only append new information at the end of the file.
- Cover object with same name in union mount: Many Unix systems support a feature to overlay multiple file systems coming from different devices in one single folder. This technique is called union mount. The contents of the different file systems will simply be merged in the destination folder. For example, you could tell macOS to overlay the contents of two different hard drives in one single folder which will then contain a “mix” of the original contents. If the two file systems contain objects with the same name, there will be the problem how to present such objects in the merged view, however. In that case, objects where this flag has been set will “cover” an object with the same name which will then become invisible and inaccessible in the merge.
- Stored with compression at file system level: In addition to the presence of a compressed data stream, the use of file compression can be flagged by this attribute.
- Object is tracked via document ID: When using modern macOS applications, it is no longer necessary to save document files manually. macOS takes care that this happens automatically, even if documents don’t have a name yet, or the open file is renamed by a different application. To organize this internally, macOS uses document identifiers independent of file names. This marker indicates that a tracking operation based on such IDs is currently active. The operating system uses this marker in order to avoid superfluous tracking via file system events.
- Object access requires special entitlement: If this attribute is enabled for a file or folder, it will indicate that under normal circumstances no program whatsoever has permission to access this object, independent of any other permission settings. Only applications that have a special entitlement embedded, which must be digitally signed with authorization of Apple, can get access. This feature is only available in modern versions of macOS and is also known as Data Vault Flag.
The following attributes have additional restrictions: They can only be set by the special Unix administrator “root” (the super-user) and they may only be unset by root when the system is additionally in single-user mode (depending on implementation).
- Locked (immutable): This setting is identical to the setting discussed in the last section, additionally protected by the super-user/single-user restriction.
- Permit append operations only: This setting is identical to the setting discussed in the last section, additionally protected by the super-user/single-user restriction.
- Archived in backup: This marker indicates that the object has been included at its current state in the last backup of the file system. Some Unix backup utilities use this marker to implement incremental backups (backup copies which only contain changes since the last backup operation). The single-user mode restriction does not apply here.
- Secured by System Integrity Protection: Access to an object with this marker is restricted. No user, not even the root super-user, has permission to modify or delete this object. Only specific programs of macOS, e.g. the Apple Installer can temporarily override this protection, or modify this attribute if System Integrity Protection is enabled.
- No removal, renaming, or use as mount point: An object with this marker must never be deleted or made inaccessible in other ways, not even by the root super-user. Modifying this attribute is also under control of System Integrity Protection.
- Object is firmlink: This feature is only supported on APFS file systems created by macOS 10.15 Catalina or later. If this marker is set, it will indicate that the related file system object is actually not stored on this volume, but is rather a link to another object stored on another volume of the same APFS volume group. macOS uses firmlinks to let folders actually stored on the writable Data volume of a system volume group appear as if they are stored are on the system volume itself (which is in fact write-protected and does not allow the presence of any user data files). Only Apple applications like the system upgrade installer or Time Machine are capable of creating firmlinks.
Press the button Close to return to the report window.
Permission Settings
After clicking the info icon next to the lines POSIX Permissions and Access Control List, Sync Checker will open an additional sheet, showing detail information about the complete set of permission settings active for the two mismatching objects. The table at the top summarizes the permission settings for the object in the first folder, the table at the bottom the settings for the object coming from the second folder.
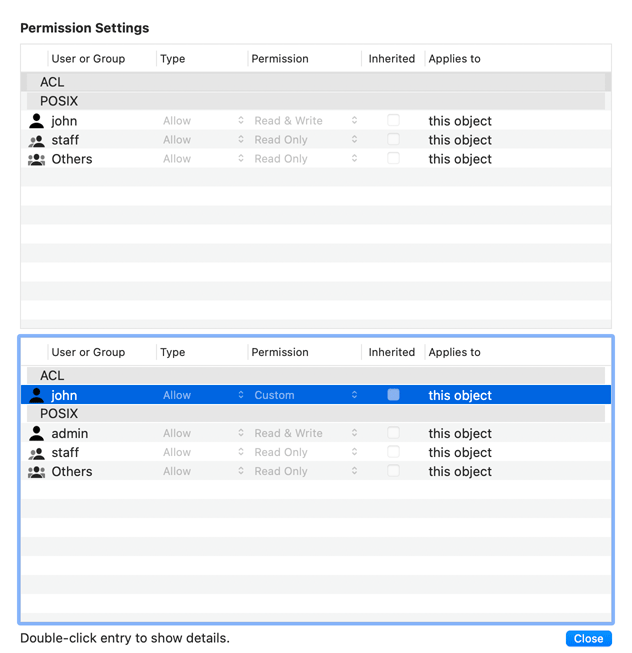
POSIX permissions and ACL entries work together to build the complete definition of permission settings that apply to a file system object. The settings presented in each table have to be read in top-down order. To determine the permissions effective for a particular user, macOS will evaluate the entries line by line and the first entry matching the user’s account and the requested right will “win”. This means if the permission settings contain contradicting entries, the entries appearing first in the table will have higher priority.
The tables contain the following columns:
- User or Group: The short names of either the user account or the group account for which the access permission in this line is to be defined. The special name Others indicates the general permission entry applicable to all other users which have not been listed in the remaining entries of the table.
- Type: The type of right defined by this entry. This can either be Allow or Deny.
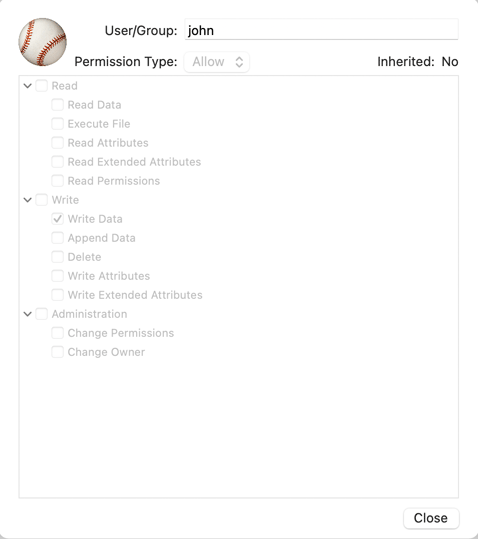
- Permission: A general description of the permission which is granted or denied. Sync Checker uses the following terms: Full Control, Read & Write, Read Only, Write Only, No Rights. macOS supports more than 98,000 additional types of detail rights which are identified by the general term Custom. If you like to see the exact definition of a custom permission, double-click the respective line in the table. Further information is given below.
- Inherited: If a check mark is set in this column, the access control entry has not been set explicitly for this object, but it has been inherited from one of the folders at some higher level in the folder hierarchy.
- Applies to: a short description in this column defines how the access control entry will be automatically inherited to objects at deeper levels in the folder hierarchy. If we don’t have a folder and we don’t have inheritance, the entry will apply to this object (the selected file system object) only. However, if inheritance is active for a folder, the entry can be inherited to files in this folder, to folders in this folder, either to objects at the current folder level, or including all objects at deeper folder levels.
Due to the complex nature of Access Control permissions, it might be necessary to show even more details about a particular entry line in the table. To do this, double-click the respective line. A drawer will open which shows the exact rights and inheritance definitions for the current object. The drawer contains the following items: The icon of the access party (user or group), the short name of that party, the permission type, the inheritance information and a list of the exact rights granted or denied by this entry.
You can close both the drawer and the sheet by pressing one of the respective Close buttons.
Extended Attributes
Each object in the file system can be associated with an unlimited number of additional data records called Extended Attributes. Each attribute has a value which can be any stream of bytes with any size. The attributes can be seen as additional content of a file next to its standard content, the data fork.
After clicking the info icon next to the line Extended Attributes, Sync Checker will open an additional sheet, showing the complete list of Extended Attributes for the two mismatching objects. The table at the left contains the attributes of the object coming from the first folder, the table at the right represents the object from the second folder.
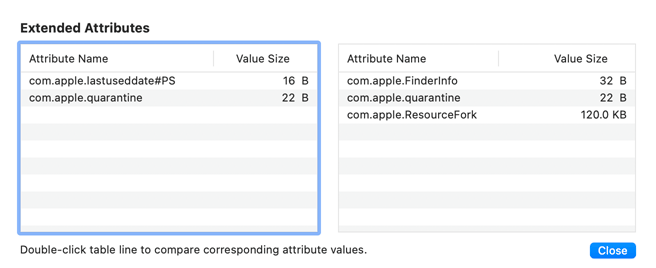
Each attribute has a unique name which is displayed in the column Attribute Name. The sequence of bytes associated with that name is called the value of the Extended Attribute. The size of that sequence is displayed in the column Value Size. The names and values of Extended Attributes are defined by the applications which created them. Applications using Extended Attributes are, for example, the Finder, Spotlight, Time Machine, Calendar Server, and several others. Sync Checker cannot “know” in general how such attributes should be interpreted or be displayed. In the general case, Sync Checker shows the attribute value as sequence of bytes, in hexadecimal notation. To see the value, double-click the respective attribute line in the table. A special window, displaying the contents of the Extended Attribute will open. The title bar of the window shows the name of the attribute. The text box at the top shows the value of the Extended Attribute coming from the object of the first folder, the box at the bottom shows the value coming from the second folder.
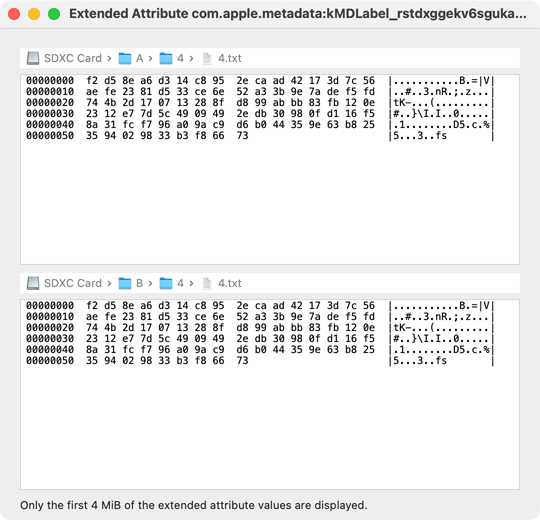
Each text box will only display the first 4 Mebibytes of the attributes (if available). If your current user account has no access permission to read the attribute, or if one of the mismatching objects is missing in one of the folders, the text There is no Extended Attribute or you have no permission to display its contents will be displayed instead. The first column in the text box is the hexadecimal offset position in the value for which the bytes are displayed (the first byte has the position 00000000). The next 16 bytes stored at that position will be shown in the line following this offset. The bytes will additionally be shown in canonical character notation, assuming that they might represent text information encoded in the ASCII standard. Characters unprintable in the ASCII standard are represented by dots (.). The 16 characters in each line are delimited by vertical bars (|).
The Extended Attribute com.apple.FinderInfo
macOS systems use a known Extended Attribute named com.apple.FinderInfo to store additional information for file system objects used by the Finder. When you double-click this known attribute, Sync Checker is capable of interpreting the value. A special window will appear.
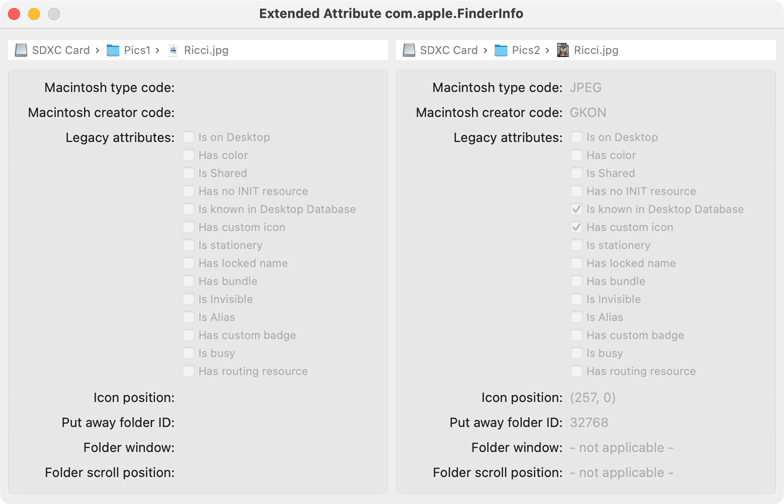
- Macintosh type code: the type code associated with the selected file. Type codes are used by the operating system to identify types of documents and selecting a matching application which is capable of opening such document types. When type codes are used, file name extensions or contents analysis won’t be necessary to identify documents. The codes are usually presented as sequence of four characters. If a code cannot be expressed this way because it contains unprintable characters, Sync Checker will show it as a sequence of four bytes in hexadecimal notation. Type codes are unique and are administered by Apple.
- Macintosh creator code: the creator code associated with the selected file. Creator codes have been used by classic Macintosh applications to identify which program has created a given file. They could be used to force the system to open a given file with a specific application, even if multiple applications have been available to open documents of the given type. Creator codes have been superseded by Uniform Type Identifiers and are deprecated technology. Modern macOS versions will no longer use creator codes to choose applications when opening documents. Sync Checker uses the same notation for presenting creator codes as it uses for type codes.
- Legacy attributes: a list of 14 attributes which can either be switched on or off. Such attributes have been used in the classic Mac OS. Only a few of them are still in active use within macOS, but they are still interpreted to maintain compatibility with old system versions. Some of them are emulated and are duplicates of attributes already discussed in the section about file flags.
- Icon position: the position in (x, y) coordinates relative to the display area of a Finder window where the icon of this object should be displayed when icon view is used.
- Put away folder ID: a reference to a folder used in classic versions of Mac OS. It does not really have meaning in macOS.
- Folder window: The coordinates, width, and height of the window the Finder should use to present this object (which must be folder) in icon view mode.
- Folder scroll position: The current position of the optional scroller when the Finder presents the folder in icon view mode.
The left box in the attribute window represents the Finder information for the mismatching object in the first folder, the right box is used for the object in the second folder.
Creating a Text Report of the Mismatch List
After pressing the button with the text icon in the upper right corner of the report window, Sync Checker will create a text document summarizing the results of the sync check operation. This text can be reviewed and additionally be printed or saved as a text processing document in Rich Text Format (RTF).
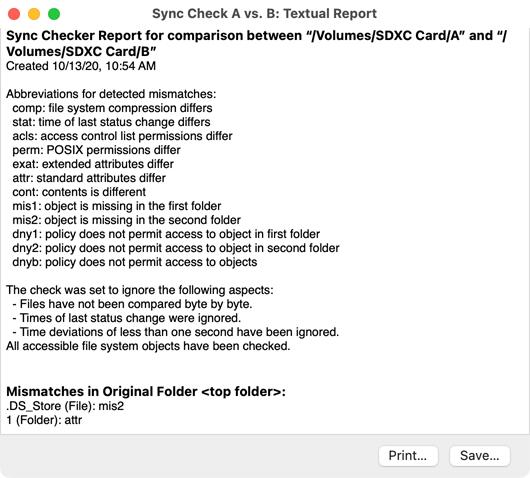
In the report, the paths of the two compared folders, the current date and time, and a legend listing abbreviations used to identify types of mismatches are presented at the beginning of the document. An additional paragraph lists the ignore settings you had used for the sync check operation. Following this section, Sync Checker will list all mismatches found, in alphabetical order of the folder hierarchy. Entries are grouped by folders. Each line lists the name of the mismatching object, followed by the list of mismatch types detected for this object pair.
Press the button Print… in the document window to print or fax the report, or to create a PDF file. Press the button Save… in the window to save the text as RTF document.
Saving and Opening Sync Checker Reports
Each report window of Sync Checker behaves like a document window you know from other macOS applications. You can save the check results to a file and review them later, even on a different computer. Sync Checker uses files with the name extension .screport as type identification.
- Select the menu item File > Save or press the key combination ⌘ + S to save the current report to a file.
- Select the menu item File > Duplicate or press the key combination ⇧ + ⌘ + S to create a copy of the current report, e.g. to save it to a file with a different name later.
- Double-click an screport file in the Finder or use the menu item File > Open… to open it.
When you review a Sync Checker report “offline”, the following restriction applies: It won’t be possible to display the values of Extended Attributes if the original objects and their attributes don’t exist on the computer where the report is displayed.
Sync Checker version 3 can open documents of Sync Checker 2 and 1. However, this won’t work in the other direction: Older versions might not always be capable of interpreting the files of newer versions.